

Data Security: Protecting Digital Information in the Modern Era
What is the most valuable asset an organization has today? It is data. Not only for organizations; protecting data is highly critical for individuals and governments as well. Modern-day businesses require organizations to rely heavily on data to make informed strategic decisions that enhance their efficiency as well as improve customer service experiences.
According to the World Economic Forum, 87% of cybersecurity leaders believe AI-related vulnerabilities are the fastest-growing cyber risks. This underscores the importance of stronger data protection and monitoring strategies.
But the rapid growth of data has also led to an increase in rise of cyberattacks, data breaches, unauthorized access, etc., that can greatly impact a business’s brand and business value.
An efficient data security strategy eliminates most of these risks. Data security involves proper data policies, techniques, and technologies to secure data from theft, loss, and unauthorized access. Let us dive deeper and explore what it entails, the common data security risks, what the best practices are to secure data, and more.
What is Data Security?
Data security is the practice of protecting data from unauthorized access, misuse, loss, or theft throughout its journey. It includes different data security tools, technologies, techniques, and policies to ensure data is safe at storage, during transit, or while being processed by applications.
Data security also checks if data is accurate and confidential, and makes data accessible only to authorized users at all times.
Types of Data That Needs Protection:
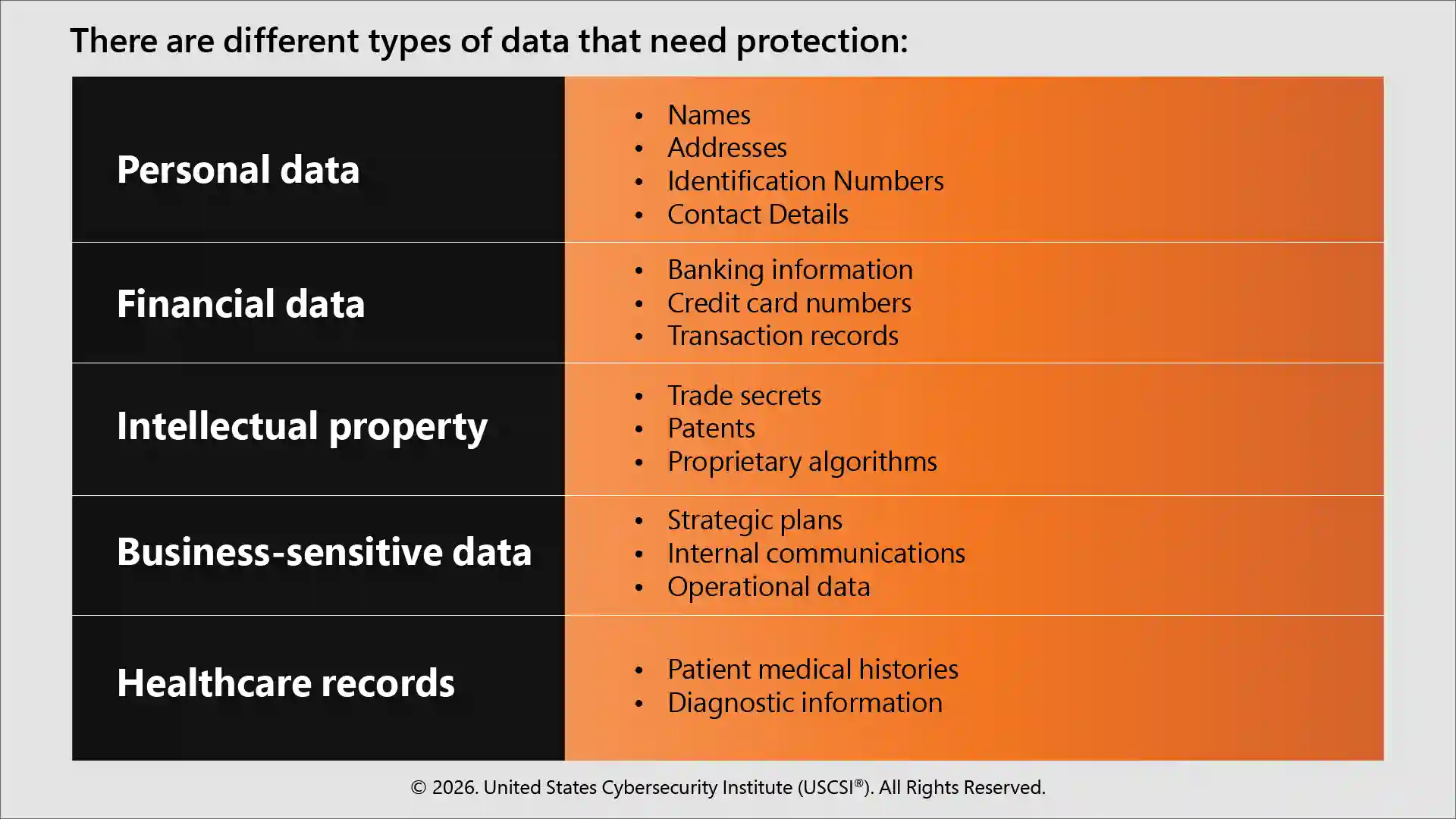
Importance of Data Security
A data breach can lead to serious consequences, including financial, reputational, and compliance issues. Therefore, data security and data privacy are important for several reasons, such as:
- Protection against cyberattacks
Cybercriminals increasingly target sensitive data for the huge value they have in the dark web market. Cyberattacks like data breaches, ransomware attacks, and hacking can lead to financial loss and operational downtime.
- Compliance with Regulations
In several countries and several industries, governments and regulatory bodies require organizations to follow strict data protection laws such as GDPR or HIPAA. Failing to comply with these standards and regulations can lead to fines and legal consequences.
- Maintaining customer trust
Customers expect that their sensitive personal information is safe with organizations using it. A data breach can erode trust as well as impact a company’s reputation. Therefore, they need to demonstrate that they are committed to securing customer information to maintain customer trust.
Common Data Security Threats
Some of the most common forms of data security threats are:
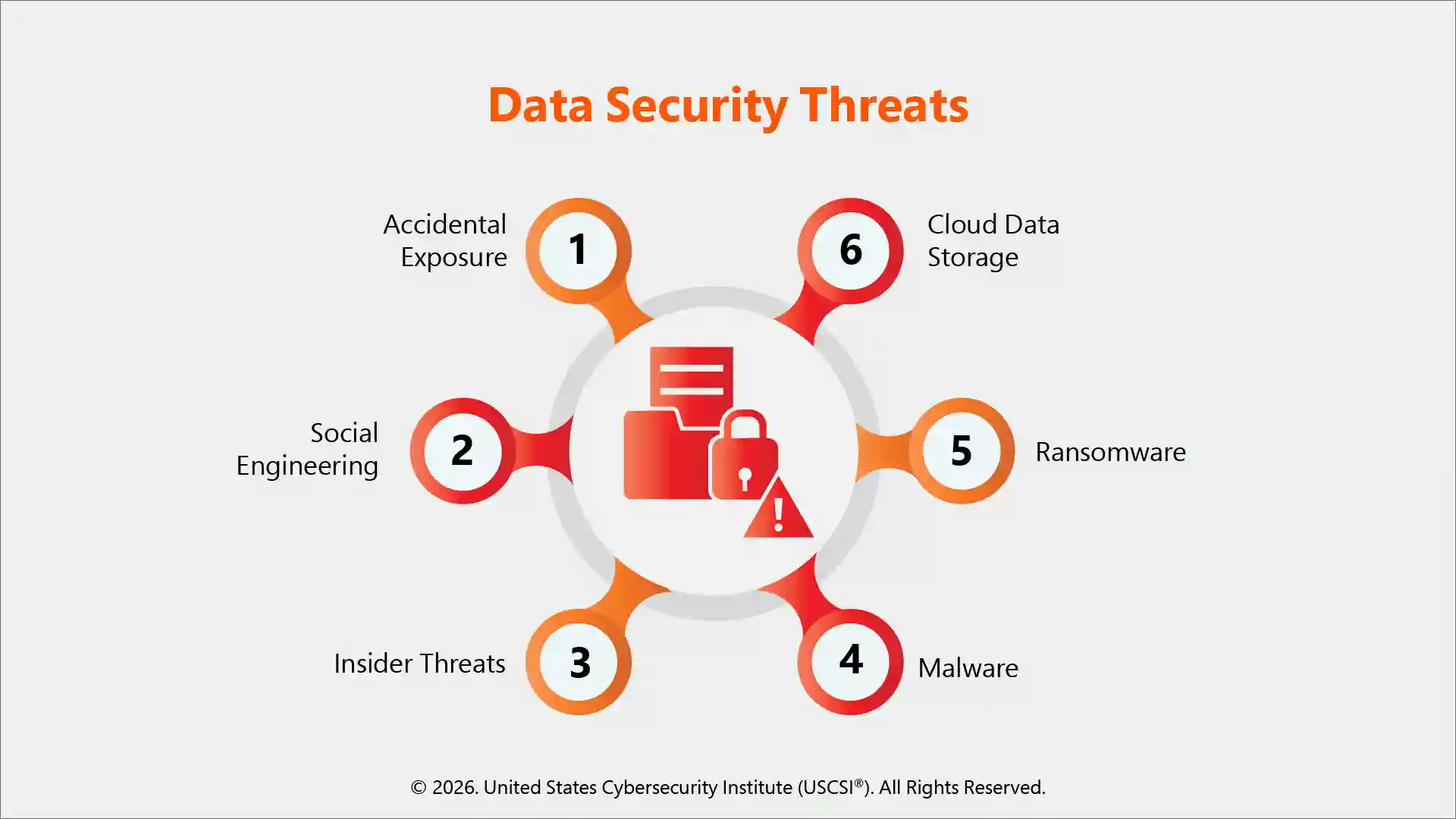
-
Data breaches
It happens when the organization’s sensitive information is accessed or disclosed without authorization.
-
Malware and ransomware
Malware (malicious software) infiltrates systems and steals or corrupts data. Ransomware is a type of malware that encrypts files and makes them inaccessible until a payment (ransom) is paid in exchange for the decryption key.
Email is the primary attack vector, as 82% of file-based cyberattacks were delivered through email (source: Check Point Security Report).
-
Insider threats
This happens when an employee, vendor, or contractor intentionally or unintentionally exposes sensitive data. It mostly occurs because of negligence, lack of cybersecurity awareness, or malicious intent.
-
Phishing and social engineering
Phishing attacks trick users into revealing sensitive information like login credentials or financial details through fake emails, websites, or phone calls.
In our comprehensive read What is a Phishing Attack? How to Detect and Stop It, learn more about phishing and social engineering attacks, how they work, their types, and prevention strategies.
Important Data Security Techniques
Organizations can implement the following data security techniques to ensure their data is well-protected:
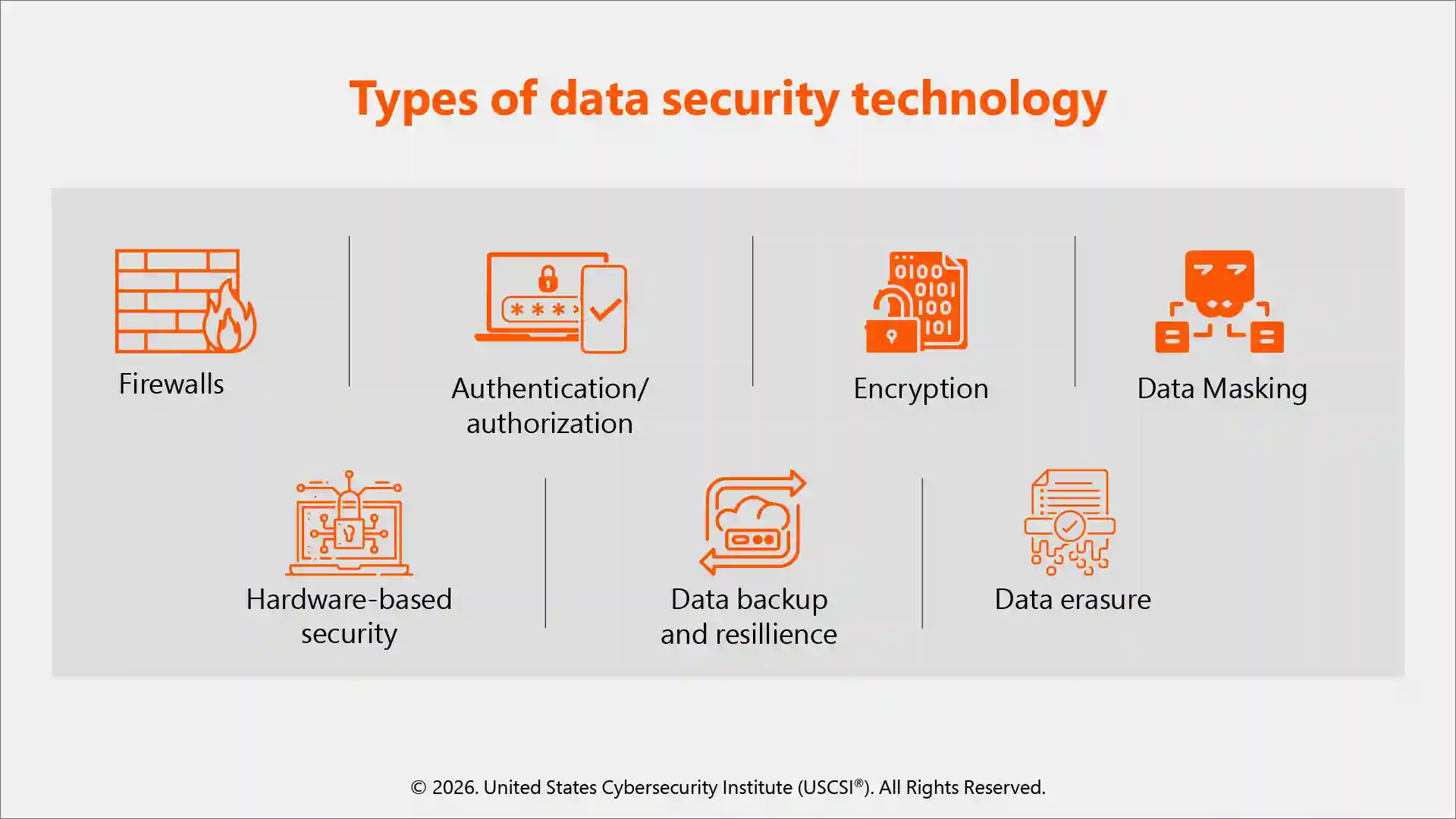
- Firewalls
It is a security barrier between internal and external networks. It uses predefined rules to filter incoming and outgoing traffic and blocks unauthorized access or threats
- Authentication and authorization
Authentication verifies the identity of the user, and authorization grants access to data to that user. Together, it ensures that only legitimate users have access only the required data
- Encryption
Encryption converts normal plain texts and readable data into cipher texts (unreadable format) using cryptographic algorithms. Only those with the correct decryption key can access the original information
- Data masking
This technique hides original information by replacing it with fictional data. Through this, organizations can use data for testing or analysis without risk of exposing confidential information
- Hardware-based security
Physical components like secure processors, hardware security modules (HSMs), or other trusted platform modules (TPMs) are used to protect cryptographic keys and information from tampering
- Data backup
Having a backup of critical information in secure storage systems helps organizations quickly restore data in case of security incidents and system failures.
- Data erasure
It is a method of overwriting existing data to remove information from storage devices. This is done to ensure data cannot be recovered if devices are sold, discarded, or reused.
Data architecture is an important element that also contributes to how data is accessed and used. This article Why Data Architecture Is Critical for Building Scalable AI Systems explains proper data architecture methods and how it is important for secure and scalable AI.
How Organizations Ensure Data Security: Best Practices
Those organizations looking to strengthen their data protection must implement the following best data security practices:
- Implement strong authentication, authorization, and password policies
- Update and regularly patch software vulnerabilities
- Conduct regular audits and risk assessments for data loss prevention
- Provide security, cybersecurity training, and cybersecurity certifications for enhanced awareness
- Apply the least privilege policy
- Use strong encryption techniques to secure data at storage and transit
- User Behavior Analytics (UBA) can help detect insider threats
This can help organizations build a strong data security posture and significantly reduce the risk of attacks.
Final thoughts!
Data security is an important element of a strong security posture. With the explosion of data and rapid adoption of data-driven decision-making, organizations need to protect their data at all costs. Implementing these best practices, such as encryption, access control, cybersecurity training, and regular audits, organizations can ensure data is safe and protected from different types of data threats.
Explore comprehensive cybersecurity certifications from the United States Cybersecurity Institute (USCSI®) that cover essential data security strategies, best practices, and implementation architecture to help you master data security, improve your organization’s state of data security, and enhance your career prospects.





