What is a Phishing Attack? How to Detect and Stop It?
Phishing attacks need no introduction. It is still the most common and dangerous form of cybercrime worldwide. Even though there is a huge advancement in the field of cybersecurity technologies, attackers find ways to exploit the most persistent vulnerability—human trust.
A single deceptive email, SMS, or phone call can trick individuals into revealing passwords, financial details, or sensitive corporate data.
Phishing is known to be the starting point for larger attacks that include ransomware infections, business email compromise, and large-scale data breaches. Nearly 25% of security incidents in 2026 involved phishing or social engineering (Checkpoint Security Report 2026). Therefore, it is important for both individuals and organizations to understand what phishing is, how it works, and how to prevent it so that they can work securely in today's digital environment.
With top cybersecurity certifications and training programs, individuals and organizations can empower themselves with essential skills and knowledge to effectively detect, report, and respond to phishing and other cyber-attacks.
What is a phishing attack?
A phishing attack is a type of social engineering attack in which cybercriminals impersonate legitimate entities and trick the victims into revealing sensitive information or performing harmful actions such as clicking malicious links, downloading infected attachments, or sharing login credentials and financial data.
According to the World Economic Forum (WEF), 77% of global survey respondents reported an increase in cyber-enabled fraud and phishing over the past year.
The image below shows how phishing works.
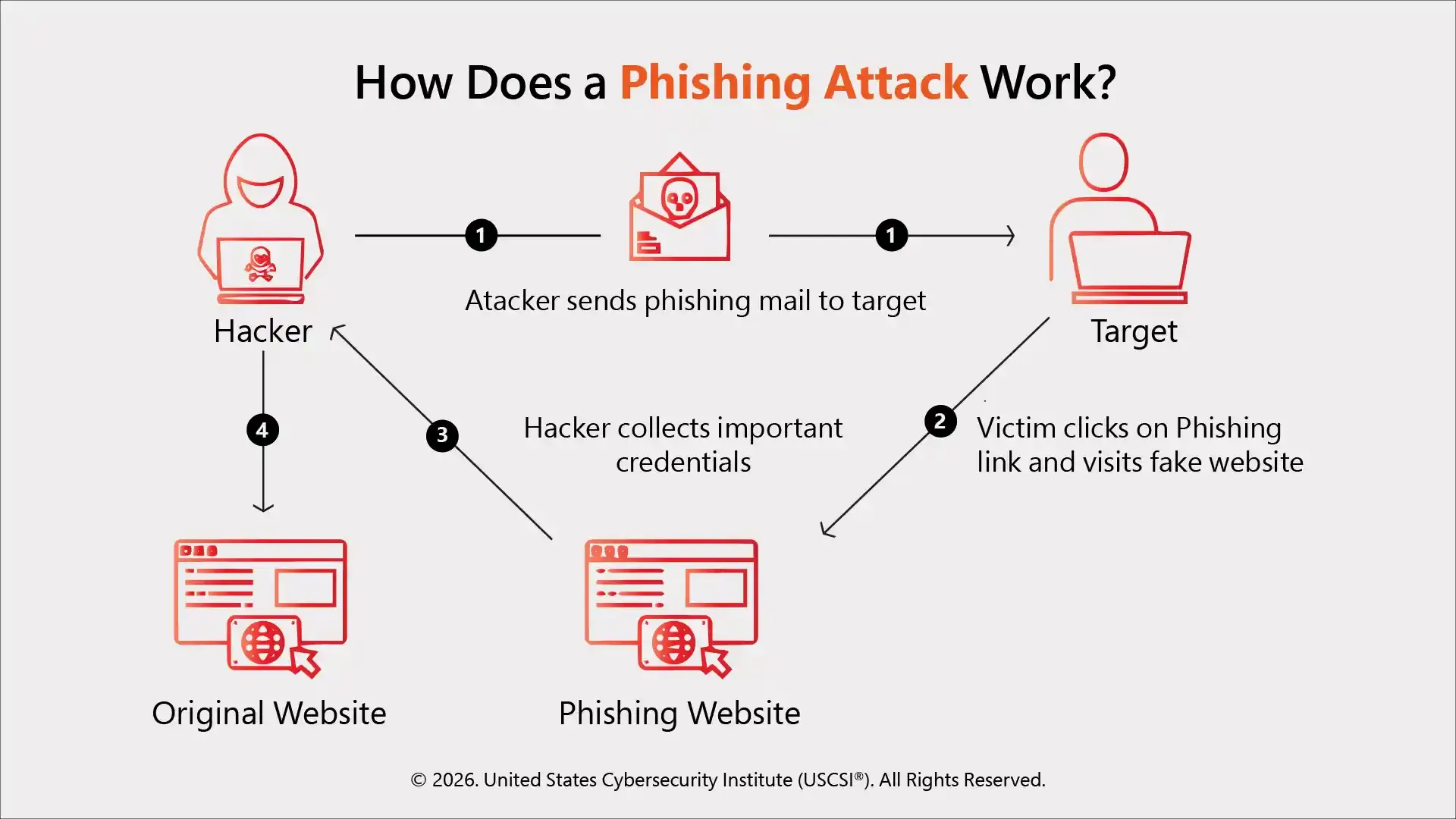
Cybercriminals usually follow three simple patterns to carry out phishing attacks:
- They create a highly convincing message that looks very genuine
- They create a sense of urgency so that victims take immediate action
- Victims unknowingly perform certain actions or execute malicious code that compromises systems.
According to Gartner, the human element will be the major cause of nearly 85% of security breaches, including social engineering and human error.
Phishing communications are specifically designed to receive and manipulate, unlike other generic spam emails.
Evolution of Phishing Attack
Phishing attacks are not new. They have existed since eternity. What once was easily detected has now evolved into AI-powered phishing that is quite impossible to recognize.
The cybercriminals earlier used to impersonate banks or payment services and ask users to verify accounting information. But today, attackers,
- Create websites that look genuine
- Spoof, legitimate email domains
- Target specific individuals instead of sending mass emails
- Leverage SMS and voice channels
- Use social media platforms
The modern phishing campaigns are highly sophisticated and difficult to recognize. On top of that, attackers use automation tools, stolen data, and artificial intelligence technologies to create more personalized and convincing messages that are much harder to detect.
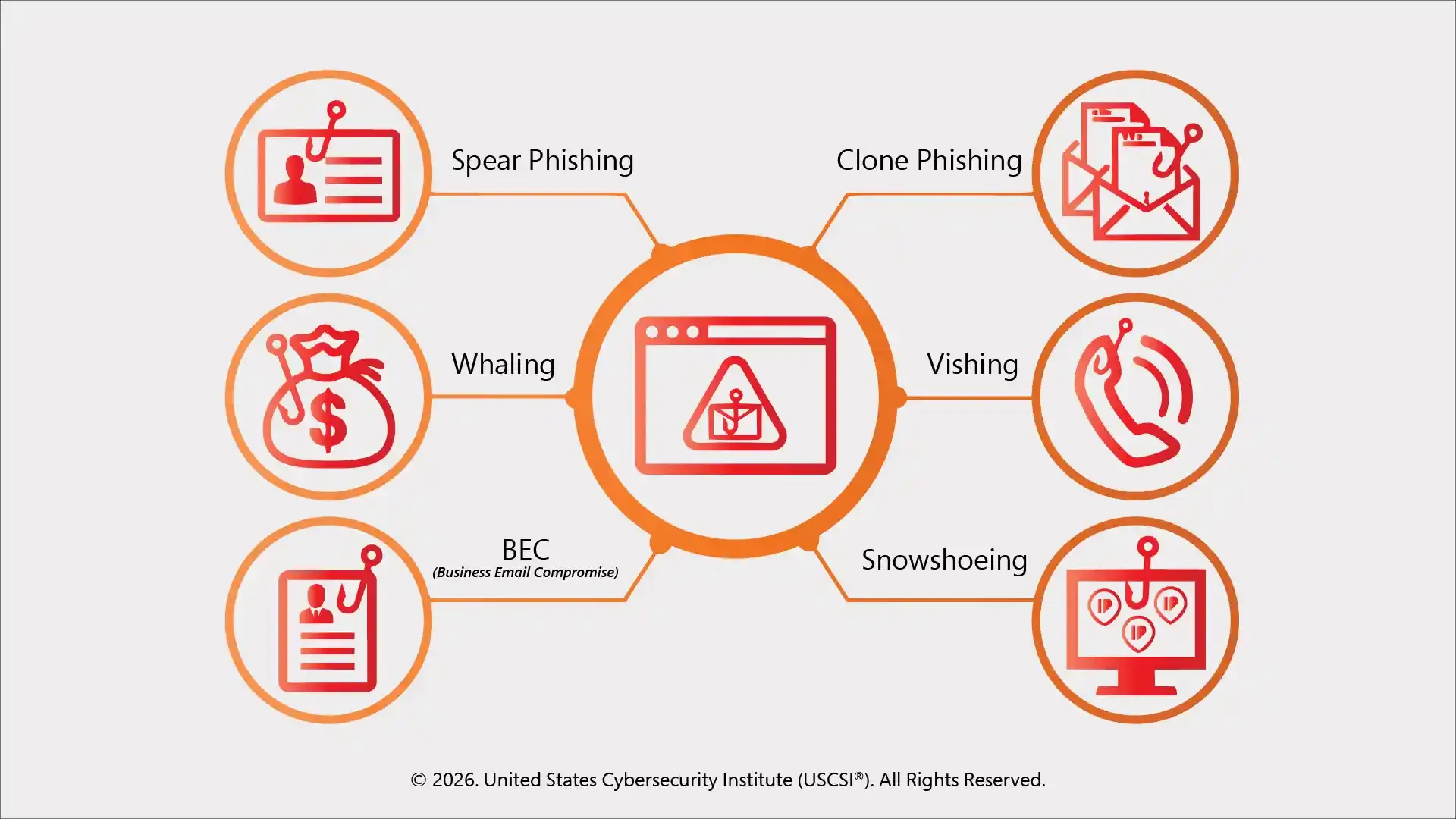
What are the Different Types of Phishing Attacks?
Phishing attacks are not limited to just email. There are different channels that cybercriminals use to target victims for greater success. The following are some common types of phishing attacks.
Phishing via SMS is known as smishing. Attackers use SMS text messages to lure victims to click on malicious links or call fraudulent numbers. These mostly impersonate delivery services, banks, or government agencies.
- Email phishing
It is the most common type of phishing attack, where attackers send bulk emails appearing to come from trusted brands like banks or other online services. These emails typically contain malicious links or attachments.
According to the WEF Report, 47% of organizations report adversaries are already using generative AI to craft more sophisticated attacks.
- Spear phishing
Spear phishing targets specific individuals or organizations. In this, attackers first research their victims and then craft highly personalized messages that increase the chances of success.
- Whaling
Whaling is a form of spear phishing that mostly targets high-level executives and decision makers. Such attacks mostly involve fraudulent financial requests or data theft.
- Smishing
Phishing via SMS is known as smishing. Attackers use SMS text messages to lure victims to click on malicious links or call fraudulent numbers. These mostly impersonate delivery services, banks, or government agencies.
- Vishing
Vishing is a phishing attack through voice calls. Target may receive calls from attackers posing as bank representatives, IT support personnel, or government officials to extract sensitive information.
- Clone phishing
In this type of attack, users get a replicated email of a legitimate email that they have previously received, but with the original link replaced with a malicious one, and keeping the rest of the message identical.
- Business email compromise (BEC)
This is a type of targeted attack in which cyber criminals impersonate themselves as senior executives or vendors to trick an organization’s employees into transferring funds or sharing confidential information. These attacks can lead to huge financial losses. Business Email Compromise (BEC) scams caused $2.9 billion in reported losses in 2026 (Checkpoint Report).
Common Phishing Techniques Used by Attackers
Attackers use different types of techniques to psychologically manipulate and carry out phishing attacks. Some common techniques include:
- Spoofed email domains: there is a slight variation in legitimate domain names so that they resemble authentic ones
- URL obfuscation: it hides malicious URLs behind shortened links
- Homograph attacks: it uses similar characters in domain names
- Fake login pages: create websites identical to original portals
- Malicious attachments: embed malware in PDFs, Word documents, ZIP files, etc.
- Create urgency: includes threats like account suspension or unpaid invoices
- Impersonate known personnel: pretend to be executives, support staff, or government officials.
Phishing techniques require quick decisions and do not give victims time to think.
Impact of Phishing Attacks
A successful phishing attack can lead to the following consequences:
- Financial losses
- Data breaches
- Reputational damage
- Operational disruption
How to detect a phishing attack?
By detecting phishing attacks early, organizations or individuals can significantly minimize/eliminate damage. These are some common signs to recognize a phishing attack:
- Suspicious sender address
Carefully inspect the sender's email address. It might include misspellings or wrong domain names.
- Generic greetings
Messages with generic “Dear Customer” greetings instead of a personalized name may be a phishing attempt.
- Urgent or threatening language
“Immediate action required” or “your account will be suspended” are designed to create panic and are signs of phishing.
- Suspicious links
Before clicking suspicious links, hover over them to see if they are unfamiliar. It can be malicious.
- Unexpected attachments
If you receive unexpected attachments from unknown senders, be cautious.
Also read: How USCSI® Cybersecurity Certifications are Closing the Global Skills Gap | Infographic to learn advantages of these credentials in boosting your cybersecurity skills and mitigating threats like phishing effectively.
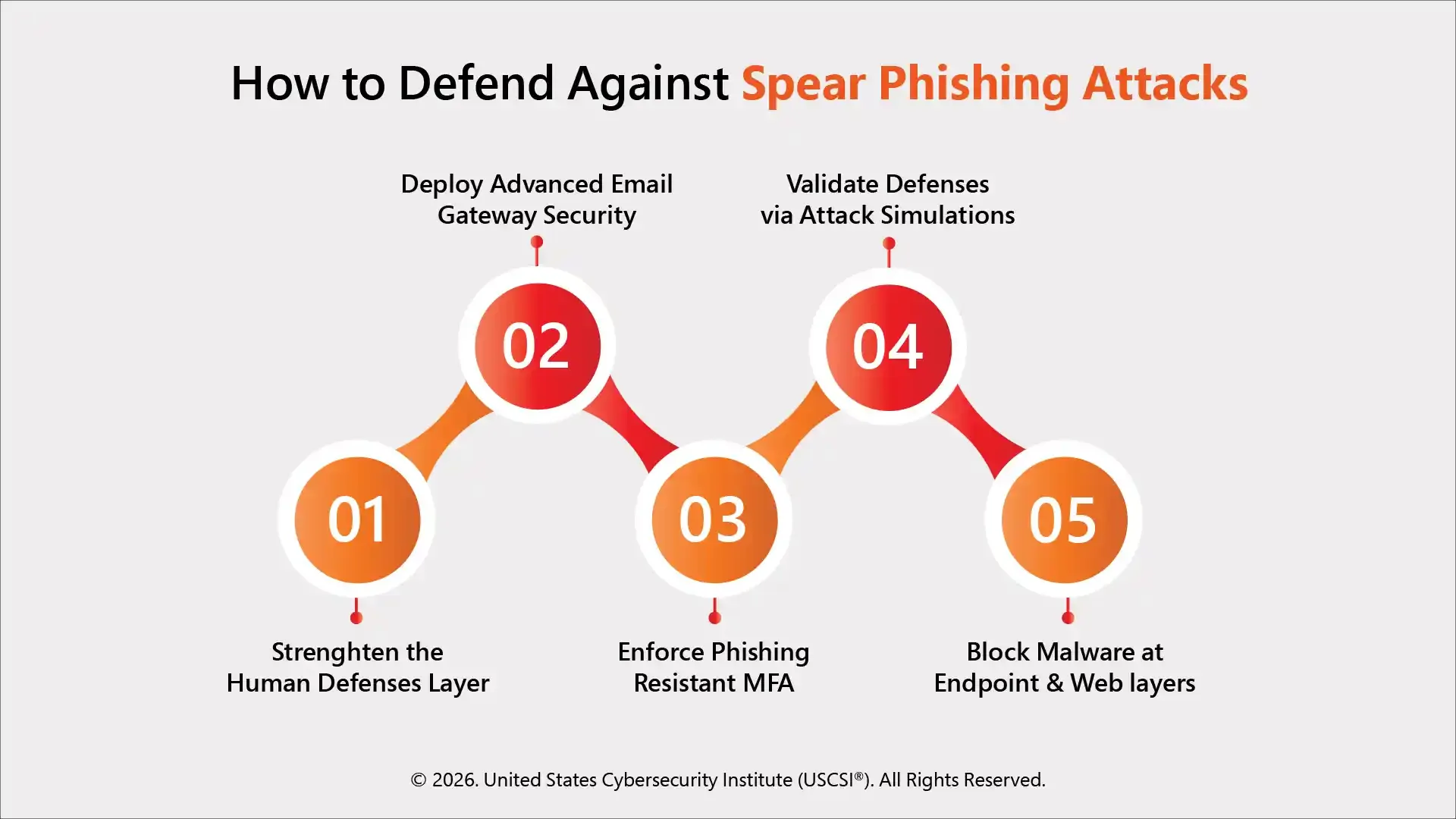
How to Prevent Phishing Attacks?
Here are some prevention techniques that require both awareness as well as technological controls.
For individuals
- MFA (Multi-factor authentication): They add an extra layer of security over passwords. So even if credentials are stolen, attackers will not be able to access your accounts.
- Password managers: Using password managers can help you generate and store strong and unique passwords
- Email filtering: Use spam filters and security software to help you detect and block suspicious messages before they reach your inbox
For organizations
- Security awareness training: organizations must provide proper cybersecurity awareness training to reduce the risk of becoming a victim of phishing attacks
- Email authentication: implement protocols such as SPF, DKIM, and DMARC that help prevent domain spoofing and unauthorized email use
- Zero trust model: Zero trust architecture will ensure continuous verification and reduce the risk of compromised credentials
- Simulated phishing campaigns: organizations can also conduct internal phishing simulations and test if their employees are aware
- Incident response planning: organizations need to have a well-defined incident response plan that can help contain damage and recover losses in case of an attack
Phishing is not the only attack individuals and organizations need to be prepared of. In this article, Preparing for Emerging Cybersecurity Threats 2026, USCSI® discusses other emerging and evolving threats you must know to keep data and infrastructure secure.
Role of AI in Modern Phishing
Artificial intelligence is completely transforming modern cyberattacks, including phishing. Today’s phishing attacks are highly convincing and harder to detect. Cyber criminals today use AI to generate context-aware phishing emails that are grammatically accurate and resemble legitimate communication.
Additionally, machine learning tools can also fetch publicly available data from social media or corporate websites and help attackers create highly personalized spear phishing campaigns.
Highly advanced AI tools can also be used for voice cloning, enabling deepfake vishing attacks where attackers impersonate executives or government officials with high accuracy. Approximately 29% of cybersecurity leaders identified the advancement of adversarial AI capabilities, including deepfakes and AI-driven phishing, as a top concern. (WEF Report)
Not just attacks, AI is also helping make defenses stronger. They power advanced security systems to use behavioral analytics and animal detection to identify suspicious patterns and block phishing communications in real time.
Final thought!
Phishing attacks today are becoming highly sophisticated and evolving at scale. They continue to be the most persistent cybersecurity threats of modern times. These attacks exploit human psychology and not technical vulnerabilities; therefore, attackers can bypass even advanced security systems.
It doesn’t mean phishing attacks are inevitable. With proper awareness, layered security controls, training, MFA, and secure policies, organizations can minimize the risk of such attacks significantly.
With USCSI® cybersecurity certifications, learn how to protect against these threats, improve cybersecurity awareness, and implement robust cybersecurity strategies to deal with not just phishing, but all kinds of modern threats.