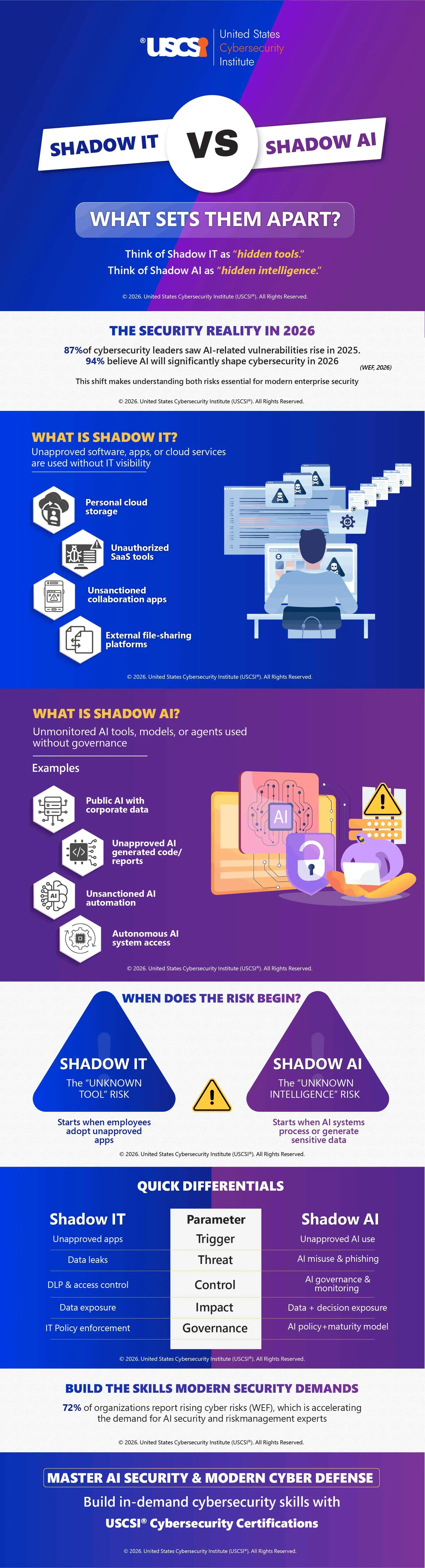
Shadow IT vs Shadow AI: What Sets Them Apart? | Infographic
The emergence of Shadow IT and Shadow AI is transforming the concept of risk management in contemporary organizations as enterprises move at a faster pace toward the spread of digital transformation.
Whereas Shadow IT can be defined as unauthorized applications running on an IT blind spot, Shadow AI can also add one more layer to the question of AI tools, autonomous agents, and generative platforms that can process sensitive information without regulation. Combined, shadow IT and AI widen the attack surface and expose organizations to data leaks, compliance losses, and phishing that is powered by AI.
The tools that are used to manage these risks in the year 2026 are beyond the conventional tools that are used in cybersecurity. The organizations should incorporate data loss prevention (DLP) systems, AI security measures, and formal management in compliance with an AI Maturity Model of Cybersecurity. Continued AI application in cybersecurity as both a defense tool and a security risk means that enterprises need to consider AI agent security policies, which observe model behavior, model outputs, and access routes.
Understanding shadow risks is crucial to professionals who intend to develop effective cybersecurity services and develop a successful career in the field of cybersecurity. Professionals can train to become skilled in the fields of AI governance, threat detection, and enterprise risk management through USCSI® Cybersecurity certifications and special training models.
Mastering cybersecurity in 2026 will include learning not just infrastructure protection but intelligent system security, because the future of cyber defense requires visibility of both tools and intelligence.
Let’s explore more about the key differences between Shadow IT and Shadow AI through the infographic.