Strengthening Enterprise Security with a Zero Trust Approach
With the expansion of organizations in digital operations, perimeter-based security cannot follow the pace of hybrid workforces, cloud computing, mobile devices, and integrations with third parties. According to industry research, 82 % of security leaders view Universal Zero Trust Network Access (ZTNA) as a critical part of their cybersecurity strategy in 2026, underscoring how essential Zero Trust has become for modern defenses. (Source: HPE)
Zero Trust focuses on the ongoing verification of all users and devices, in contrast to the traditional models that presuppose trust toward the network. The change is assisting organizations to reevaluate the concept of security, minimize threats, and enhance the security of sensitive information. In this blog, let us explore how adopting a Zero Trust approach can strengthen enterprise security and what steps organizations can take to implement it effectively.
Why Modern Organizations Are Moving Toward Zero Trust
The shift to Zero Trust is motivated by the accelerated change in the digital infrastructure. The traditional network boundaries are no longer effective in businesses where remote workforces, hybrid cloud environments, and interconnected applications are the new business staples.
Hackers tend to break into the system by using compromised credentials, phishing/weak endpoints. When they get in, they can move laterally and reach vital systems in case there are no adequate controls.
Zero Trust mitigates this risk by authenticating access based on identity, device health, and context. Restricting access and constantly tracking the activity, organizations will be able to identify suspicious activity sooner and enhance the overall security.
Core Principles Behind the Zero Trust Framework
The knowledge of the key concepts of the Zero Trust framework will enable organizations to develop an efficient security plan.
The most significant principles are the following:
- Verification: Before accessing the resources, all users, devices, and applications should be verified.
- Real-time monitoring: Security systems continuously analyze the actions of users and the state of the devices.
- Assume breach mindset: Security teams put in place systems that are based on the assumption that attackers might already be in place.
- Micro-segmentation: The networks and resources are subdivided into small units to avoid horizontal movement.
The combination of these principles generates a strata-like security environment that is much more difficult to breach by attackers.
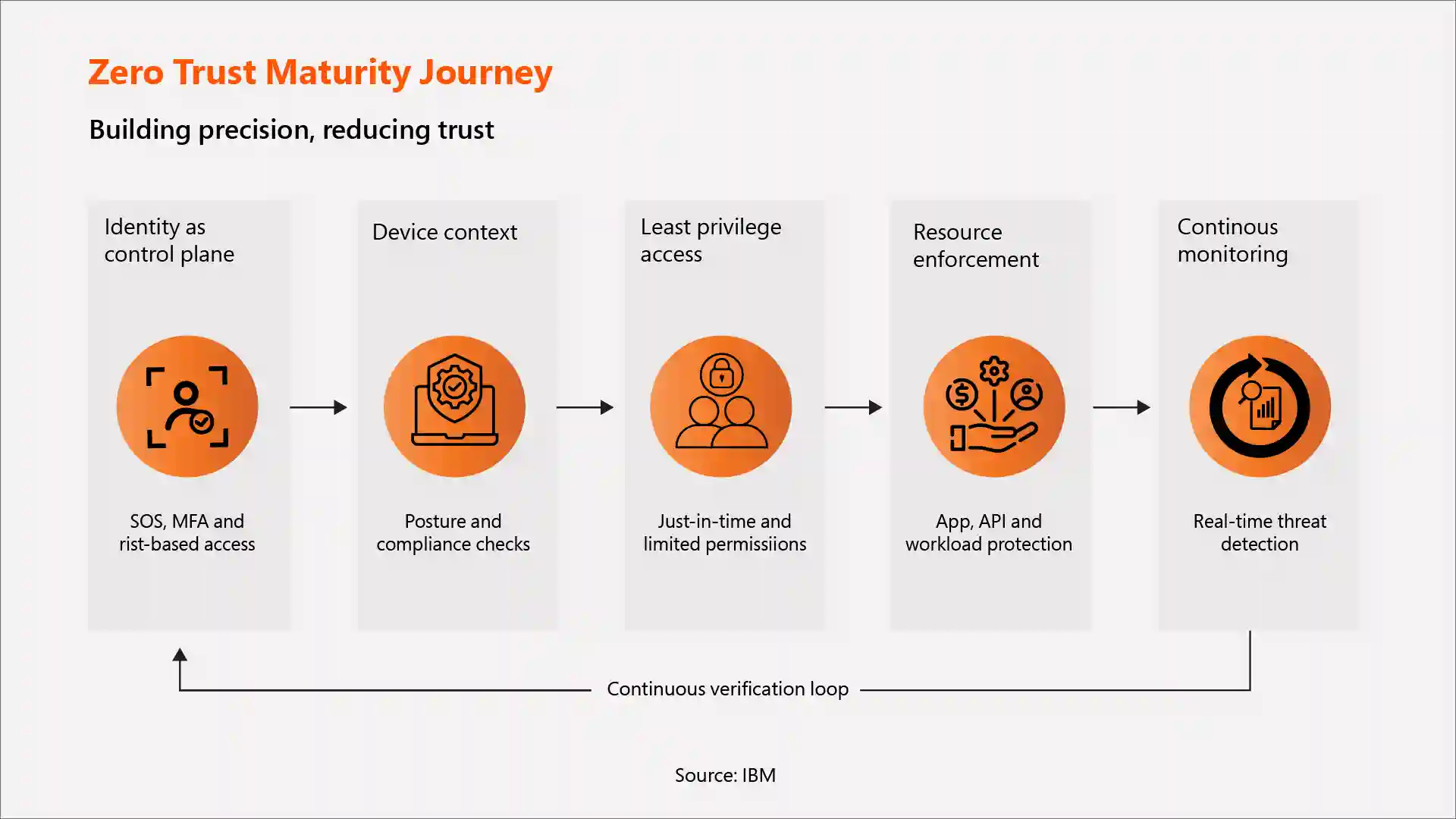
How to Implement Zero Trust: Step-by-Step Approach
Zero-trust architecture implementation will not be an immediate deployment but a progressive change of security practices. Organizations usually use a gradual nature of dge
-
Establish Identity as the Security Foundation
Zero trust security strategy starts with identity in the first stage. All users, applications, or systems seeking access are subject to verification before accessing organizational resources.
Key actions include:
- Installing multi-factor authentication (MFA) for all individuals.
- Implementing risk-based policies of authentication.
- Identity governance and access management solutions are used.
- Tracking authentication operations of suspicious behavior.
Aligning identity with security can help organizations to make sure that only the authenticated and authorized people can enter.
-
Evaluate Device Context and Security Posture
Upon identity verification, Zero Trust assesses the device that is seeking access. They should meet the security requirements before they are permitted to communicate with applications or networks.
Important checks include:
- Posture validation of devices and security.
- Tracking patch levels and updates of operating systems.
- Making sure that endpoint protection tools are functional.
- Limiting the entry to unmanaged or dangerous devices.
The layer is used to ensure that the compromised or insecure devices do not open up an entry point to attackers.
-
Enforce Least-Privilege Access
After identity and device trust have been validated, organizations must only allow access to what is needed to perform a particular role or task.
Best practices include:
- The use of role-based access control (RBAC).
- Access to sensitive resources is on a just-in-time basis.
- Only necessary systems should be permitted.
- Carrying out periodic user privilege reviews.
Least-privilege access significantly reduces the risk of attackers moving laterally across the network.
-
Protect Applications and Resources
Zero Trust deals with securing the applications rather than the network as a whole. The users must be restricted to access only specific resources to which they have authorization to use.
The security measures might involve:
- Application-level access using Zero Trust Network Access (ZTNA).
- Using application, API, and workload security controls.
- Isolating critical systems by segregating networks.
- Imposing user role and device context policies.
This is a method of reducing exposure as well as securing sensitive resources
-
Continuously Monitor and Adapt Security Controls
Zero Trust is not a verification procedure. This is done through constant monitoring, which allows threats to be resolved in a short time.
Organizations may enhance visibility by:
- Live user and network performance.
- Implementation of security information and event management (SIEM) systems.
- Identifying anomalies with the help of AI-powered analytics.
- Automating responses to potential security attacks.
Complementing these capabilities, USAII's analysis of SIEM, SOAR, and AI, artificial intelligence, enhances these platforms by automatically correlating alerts, summarizing incidents, and recommending response actions, helping security teams prioritize threats faster and close gaps that traditional monitoring typically misses.
Integrating AI into your SIEM and SOAR stack is no longer optional; it is quickly becoming a baseline expectation for mature Zero Trust environments.
Cybersecurity Tools Supporting Zero Trust
Modern cybersecurity solutions are important in the facilitation of Zero Trust policies. The mix of technologies is usually employed by organizations. These security technologies are collaborative to form a safe and policy-led setting.
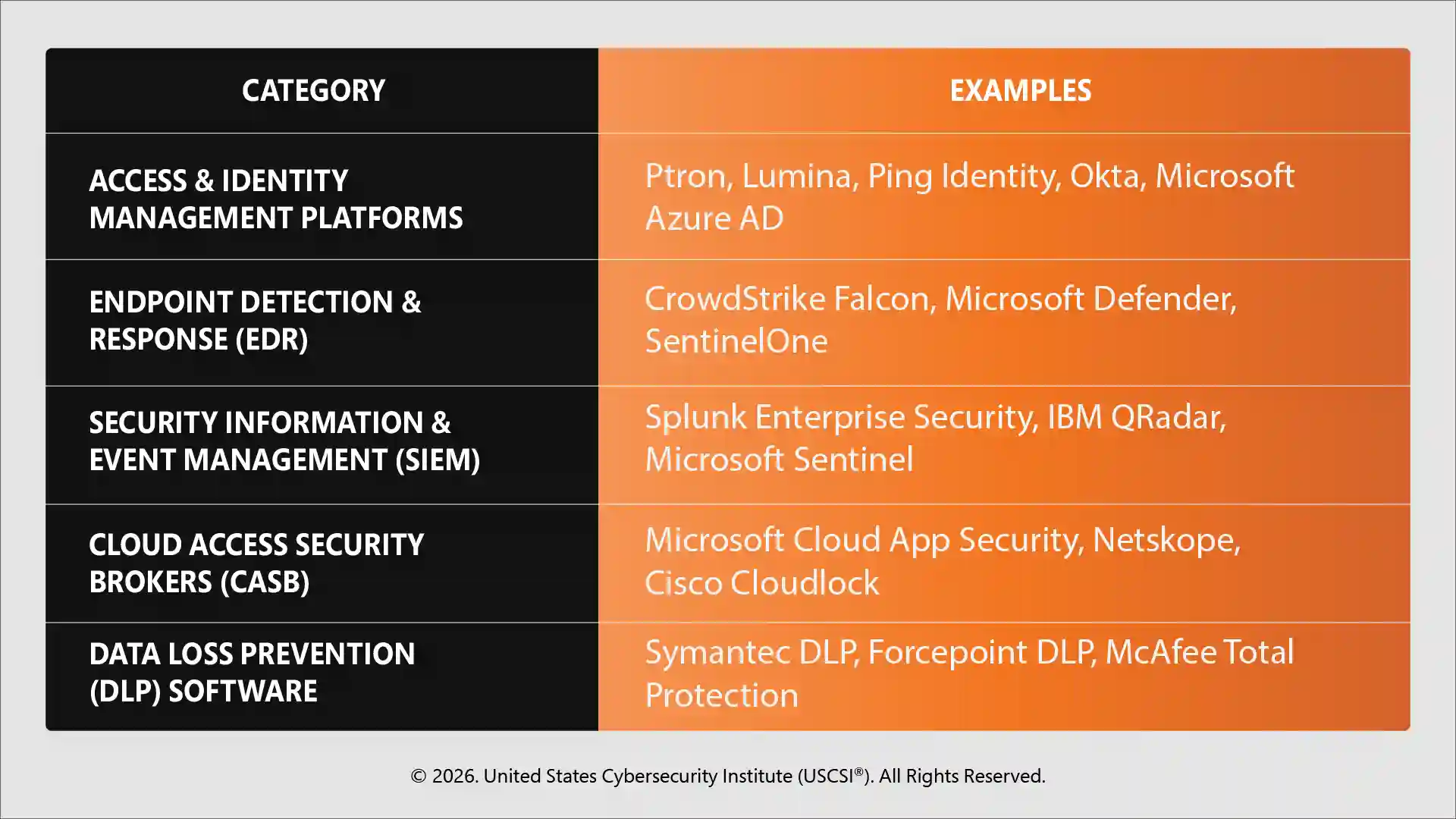
Also Read: Must-Have Cybersecurity Tools for 2026
Growing Demand for Zero Trust Skills in Cybersecurity
The role and demand for cybersecurity experts with the expertise to develop the current security architecture, identity management, and cloud security are increasing with the implementation of Zero Trust systems in organizations. Building expertise in Zero Trust architecture, security automation, and threat detection is essential for advancing a career in cybersecurity.
Certified Senior Cybersecurity Specialist (CSCS™) certification program from the USCSI® equips professionals with practical, strategic, and technical skills needed to implement robust security architectures.
Not only does it validate your professional qualification, but it also makes you ready to design, implement, and run Zero Trust systems with proper effectiveness to keep your organization at the forefront of the changing cyber threats.
The Future of Cybersecurity Is Built on Zero Trust
The nature of cyber threats is becoming more advanced, and the growing digital infrastructures are requiring flexible security models. The Zero Trust approach does not assume implicit trust; it implements strict access controls and continuously monitors activity, which reduces risk significantly. Zero Trust is not a technical upgrade, but it is a strategic choice to create extremely resilient, future-friendly cybersecurity.





