

Why is IT-OT Cybersecurity Convergence Critical for Modern Enterprises?
Cybersecurity is traditionally meant to protect important hardware assets of organizations, including servers, laptops, databases, and cloud infrastructure. But in the last few years, rapid digitalization of industries has completely transformed the actual meaning of cybersecurity. Today, the attack surface is not limited to securing just networks and devices; organizations must secure their ‘operational technology (OT)’ systems, i.e., the systems that manage physical processes such as in manufacturing, energy, transportation, utilities, etc.
According to the WEF Cybersecurity Outlook Report 2026, 42% of organizations include IT/OT convergence in their risk strategy.
The convergence of IT and OT environments has given rise to a new frontier in cybersecurity that powers automation, real-time analytics, and improves operational efficiency as well. In this article, let us understand what IT and OT cybersecurity is and how organizations can benefit from its convergence for maximum security.
Understanding IT and OT Systems
Information Technology (IT) refers to the computing systems that store, process, or transfer business data.
IT systems include:
- Corporate networks
- Servers
- Database
- Applications
- User devices such as laptops, smartphones, etc.
So, IT Cybersecurity is all about protecting these components of IT systems and sensitive information, and ensuring data is protected and accessible only to authorized users.
Operational Technology (OT), on the other hand, is a combination of hardware and software that monitors and controls physical processes in industries.
OT systems include technologies like:
- SCADA systems
- Programmable logic controllers (PLCs)
- Sensors
- Actuators
- Robotics, etc.
All these components are used in factories, power plants, and transportation infrastructure.
According to GuidePoint Security’s GRIT 2026 Ransomware and Cyber Threat Report, the number of ransomware victims increased by 58% year over year. The manufacturing sector was the most targeted industry, accounting for 14% of all attacks, followed by the technology sector at 9% and retail/wholesale at 7%, indicating a growing focus on industries heavily reliant on operational and industrial systems.
While IT systems handle digital information, OT systems are related to the physical world. So, if there is any attack on an OT system, then it can potentially disrupt manufacturing lines, cause power outages, damage equipment, and even threaten human safety.
In conjunction with this, IoT security is also very important. We have talked about the same in another detailed article What is IoT Security? Threats, Risks, and Solutions Explained? Read this for detailed insight into IoT Security.
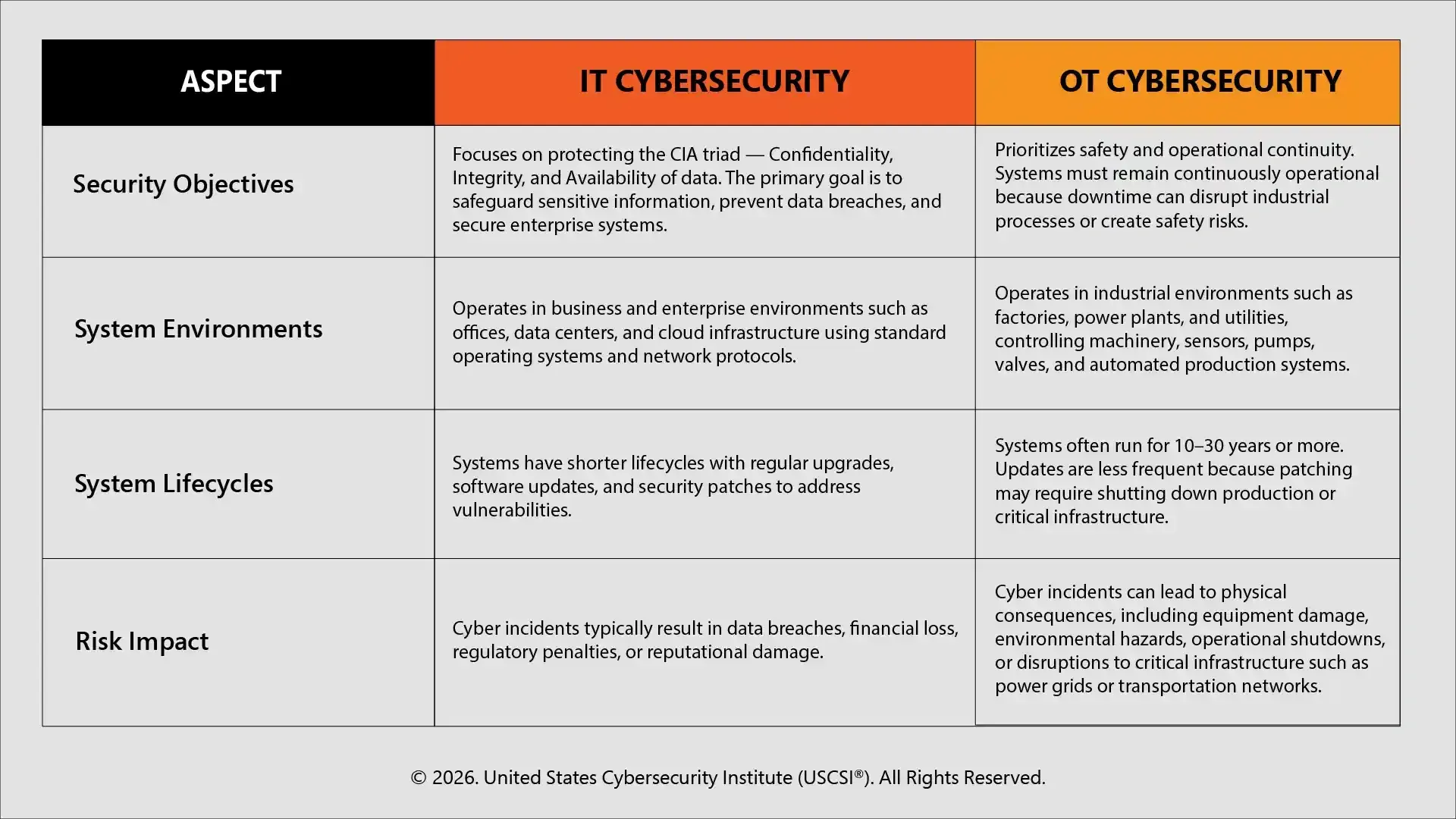
Key Differences Between IT and OT Cybersecurity
Though IT and OT cybersecurity have the common goal of protecting systems from cyber threats, their priorities and approaches differ significantly. Let’s understand their differences.
With comprehensive Certified Cybersecurity General Practitioner (CCGP™) cybersecurity certification programs from USCSI®, you can learn about IT security and OT cybersecurity in detail.
The Growing Importance of IT and OT Convergence
Historically, OT systems worked separately from external networks in an altogether different environment. But with the rise of Industry 4.0, smart manufacturing technologies, and the industrial internet of things, OT systems have been increasingly connected with organizations’ IT networks for better monitoring and analytics.
This integration, of course, offers greater efficiency in terms of operational capabilities, but it also increases the attack surface and risk of different kinds of cyber threats. They introduce new entry points for attackers to exploit when connected to corporate networks.
For example, the convergence of IT and OT systems may often constitute numerous connected devices from different vendors. Many of these devices/vendors may be using only consumer-grade technology and may not have industrial-level security controls. This increase in IT/OT convergence also leads to an increase in access points, further increasing the risk of malware infections, ransomware attacks, insider threats, etc.
The latest cybersecurity training programs now focus on these trending topics and empower professionals with essential cybersecurity and IT skills needed to implement IT and OT security properly.
IT – OT Cybersecurity: The Future of Infinite Possibilities
Looking into the future, we can say that cybersecurity will be more about integration and protection of both IT and OT systems.
Industries today are opting for smart manufacturing, Industrial Internet of Things (IIoT), and automation. This leads to significantly reducing the gap between digital systems and physical infrastructure. And this convergence requires a holistic cybersecurity framework that addresses both corporate networks and industrial controls.
So, in the future, we will see organizations rapidly adopting AI-powered threat detection, Zero Trust Architecture, real-time monitoring, and other advanced cybersecurity tactics to secure these interconnected environments.
The coming years will witness both IT and OT teams working together, sharing cybersecurity tools and knowledge, ensuring compliance with regulations and standards, and strengthening critical infrastructure.
Emerging Threats in IT and OT Cybersecurity
Both the corporate and industrial environments are the prime targets for cybercriminals and nation-state attackers.
- Growing Exposure of Industrial Systems
The number of industrial control systems dependent on the internet is increasing rapidly. Reports highlight that the number of industrial devices exposed has increased, that have increased the potential attack surface for Operational Technology (OT) devices.
- Rising Attacks on Critical Infrastructure
Critical infrastructure sectors such as manufacturing, energy, utilities, transportation, etc., are increasingly targeted by cybercriminals. Attacking these systems means directly halting production, interrupting essential services, and causing major financial damage.
- Sophisticated Ransomware Campaigns
For ransomware groups, industrial control systems and operational networks are now among the most preferred targets, as it causes maximum disruption. Attackers disrupt normal operations and increase pressure on organizations to pay ransom demands for the quick restoration of production/services.
- IT-OT-IoT Convergence Risks
Integration of these devices, though, helps with better automation and real-time data exchange; it also creates several entry points that attackers can use to infiltrate networks and move laterally to disrupt other critical operational systems.
Top Challenges in Security IT and OT Environments
- Legacy infrastructure
One of the biggest challenges is old and outdated systems that most organizations are still using, designed decades ago. They do not have any built-in security and can be easily breached
- Limited patch management
Most of these systems operate continuously without any break, which makes applying patches or security updates difficult, as it can lead to operational downtime. This longer patch cycle increases security risks
- Visibility gaps
Another important challenge is the lack of visibility for OT systems. It often becomes difficult to identify vulnerabilities and monitor threats without having accurate asset inventories.
- Organizational Silos
In simple terms, IT and OT teams work separately, have different priorities, and different functions. This difference creates communication gaps and reduces response efforts.
How to Address Risks: Best Practices for IT and OT Cybersecurity
Did you know, AI-enabled security operations can lead to 95% fewer manual security tasks and up to 10× faster incident response times, significantly improving threat detection and remediation capabilities (Source: Google Security Report). Now that we know what the common security challenges are, here are some ways to address them:
- Network Segmentation
There should be different networks for IT and OT. It will minimize the risk of cyberthreats spreading from one system to another
- Continuous Monitoring
Cybersecurity professionals must leverage advanced tools and AI-powered cybersecurity tools to detect anomalies, identify threats early, and respond to them promptly
- Clear Visibility
Those organizations that can maintain clear visibility for their inventories of IT and OT systems can easily identify if there are any security breaches and manage risks effectively.
- Zero Trust Architecture
Zero-trust principles are a great way to enhance cybersecurity posture. It ensures that no device, user, or application is trusted by default and needs proper authentication and authorization to access critical systems.
- Cross-Team Collaboration
By improving the coordination between themselves, IT and OT teams can help organizations improve their overall security strategies as well.
For cybersecurity professionals, using the latest tools and techniques can result in great results. Read SIEM, SOAR, and AI: Can Cybersecurity Professionals Get the Promised Results to learn about these security tactics and how they help enhance overall security posture.
Concluding Thoughts!
It is the era of smart factories, connected infrastructure, cloud environment, digital-twins, and AI-powered automation. What makes this era unique is the rapid integration of IT and OT systems together to enhance business operations. This convergence has huge operational benefits, but cybersecurity risks associated with it cannot be ignored.
Therefore, organizations need to adopt a modern cybersecurity approach and protect both information systems and industrial processes. Emerging technologies such as AI-driven threat detection, automated response systems, and network segmentation can help organizations truly enhance their cybersecurity posture.
Organizations and professionals looking to master these advanced IT and OT cybersecurity must explore the highly recognized and credible USCSI® cybersecurity certifications covering the latest industry-relevant cybersecurity curriculum, skills, and practices. Be it designing best IT security practices or implementing security strategies across OT systems, USCSI® certifications offer the perfect blend of skills and knowledge required to strengthen an organization's security and grow in an individual's career path.





