Data Risk Assessment in 2026: A Step-by-Step Practical Approach
Data has emerged as the core of contemporary organisations, but along with that comes more risk. With data in transit between systems, users, and platforms, which, under many circumstances, is out of view, ensuring its protection has become a more complicated task, particularly with the emergence of the cloud, third-party applications, and AI-oriented actions.
The World Economic Forum Global Cybersecurity Outlook 2026 states that more than 87% of organizations stated that AI-driven cybersecurity threats have been on the rise, with a significant number already experiencing data leaks linked to emerging technologies.
This shows the importance of ensuring that data risks are actively identified and addressed instead of responding to them when they have caused harm.
This blog will stepwise guide you on how to conduct a data risk assessment and provide practical information to enhance your data security assessment process.
What is a Data Risk Assessment?
A data risk assessment method is a structured method of identifying, analyzing, and reducing data risks in its lifecycle. It concentrates on the extraction of the location of data, its utilization, the authorized individuals who can access it, and what could go wrong if it is exposed or misused.
In comparison with a general assessment of cybersecurity risks, it is highly oriented towards data itself; it becomes the key to successful data governance and compliance, information security audits, and long-term data protection plans.
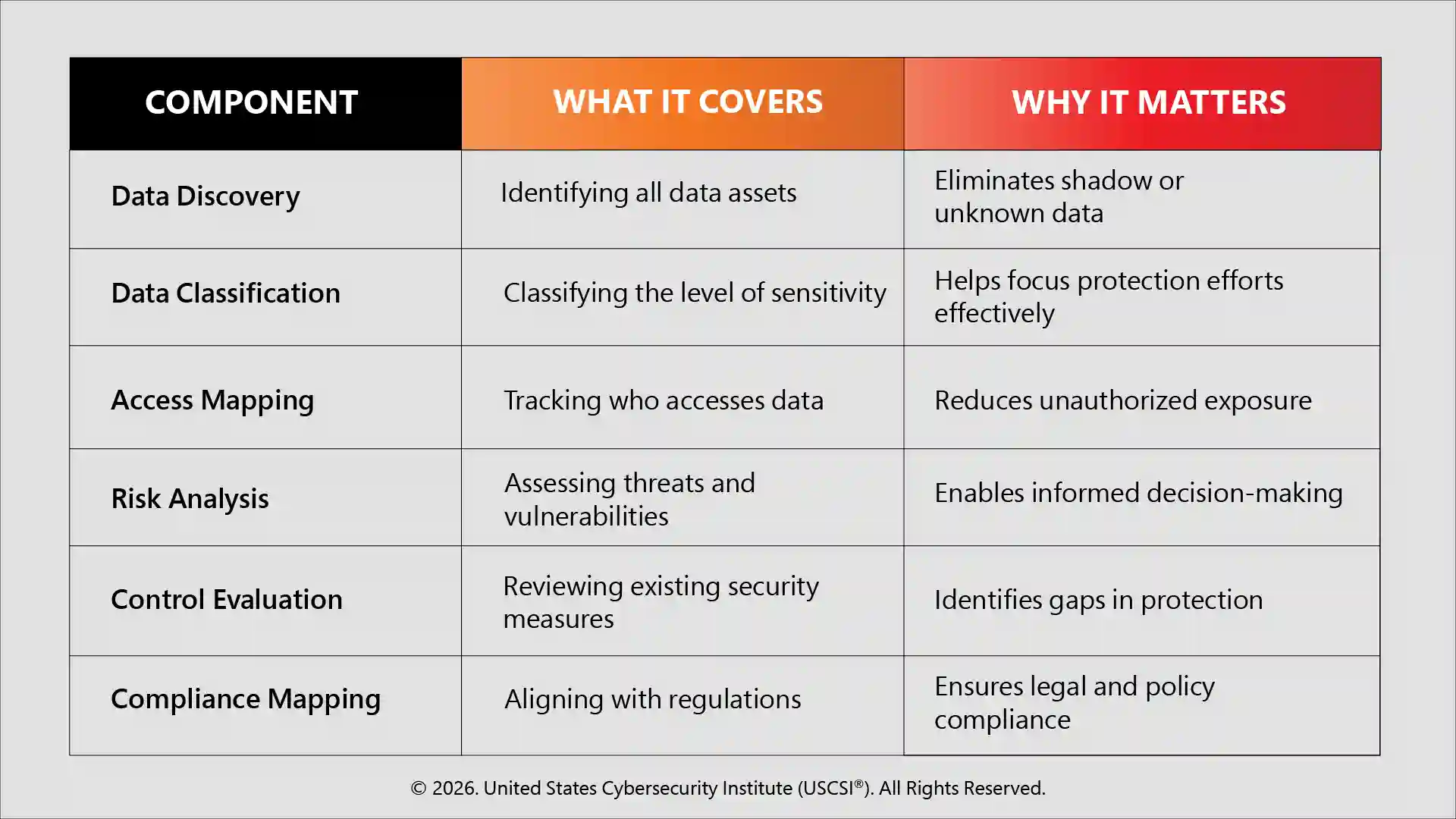
Core Components of a Data Risk Assessment
A data risk assessment is based on a collection of major elements that offer data risk identification and management with visibility, control, and structure. All these factors combined provide organisations with the opportunity to secure sensitive data, achieve exposure minimization, and compliance.
Step-by-Step Data Risk Assessment Process
-
Define Business Context and Risk Scope
Begin by knowing what information is really important to your organization. Rather than looking at all the data as equal, determine what datasets have a direct effect on revenue, its operations, or compliance. This will keep your risk assessment framework in line with actual business priorities.
-
Perform Advanced Data Discovery
Move beyond simple data inventory management and discover data in all of the environments: cloud-based services, SaaS applications, the endpoints, and even the uncontrolled storage systems. The aim is to unearth concealed or duplicate information, which in most cases is a silent risk.
-
Classify Data Based on Context and Sensitivity
Apply recent data classification techniques that go beyond simple labels by taking into account the use, location, and level of exposure of data. This will provide more precise prioritization and effective protection of sensitive data.
- Classify data according to sensitivity (PII, financial, intellectual property)
- Take into account usage trends (active, shared, archived data)
- Assess exposure risk (external vs internal systems)
- Grant the appropriate access and security controls based on the classification.
- Recurrently audit and revise classifications as data usage changes.
-
Map Access and Identity Relationships
Analyze who has access to what data, including employees, vendors, and systems. One of the most common causes of breaches is poor access control, so this step is highly important to ensure the security of the enterprise, and it usually needs the assistance of an IAM Specialist.
-
Identify Real-World Risk Scenarios.
Rather than listing abstract vulnerabilities, think in situations.
- What if a user account is compromised?
- What happens in case of a breach of a third-party system?
- What is the case with the accidental sharing of sensitive data?
Such a strategy will help make your cybersecurity risk assessment more feasible and practical.
-
Evaluate Existing Security Controls
Determine the real-life applicability of your existing data privacy settings, not only in theory. This helps in the detection of the discrepancies between the security measures taken and their performance.
- Ensure that encryption is applied across all systems and data states
- Test the ability of monitoring tools to identify abnormal data actions in real-time.
- Test incident detection and response capabilities
- Determine weaknesses or improper settings of the developed security tools and policies.
-
Prioritize Risks Using Impact and Likelihood
Not everything is a risk that must be acted upon quickly; prioritization allows one to concentrate on the most important things.
- Determine financial, operational, and reputational impact.
- Assess the possibility of every risk.
- Prioritize using a basic risk Matrix.
- Start by focusing on high-impact, high-probability risks.
This maintains data risk management as being focused and efficient.
-
Implement Focused Data Protection Strategies
Use specific data protection measures, including:
- Multi-factor authentication
- Data encryption
- Network segmentation
- Implementation of information protection equipment for data loss prevention.
The trick is accuracy, protection of vital data without unnecessary complexity of systems.
-
Align with Governance and Compliance Requirements
Make sure that your processes are consistent with regulatory requirements and internal policies to ensure that you are consistent and accountable throughout your data environment. Effective data governance and compliance help not only to minimise legal risks but also to establish structured, disciplined operations.
- Ensure that your data practices align with laws such as GDPR, ISO standards, and industry-specific legislation.
- Always implement internal policies in every system and every team.
- Keep accurate records of audits and compliance audits.
- Periodically revise governance systems according to new rules.
- Employees should be trained on compliance in their day-to-day activities
-
Continuously Monitor and Improve
Data environments are dynamic, and new risks are created as a result of cloud changes, third-party integrations, and user behavior. Periodical surveillance is used to identify abnormal access history and possible intrusions in advance.
In order to remain functional, automated tracking, periodic information security audits, and updating controls according to emerging threats and compliance requirements should be used by organizations, making sure that the process is adaptive and resilient in the long-term.
Common Mistakes to Avoid in Data Risk Assessment
Even properly designed tests fail because of the gaps in the execution. Some of the common mistakes include
- Considering the process a one-time activity rather than a continuous one.
- Overlooking the unstructured or shadow data during the discovery stages.
- Excessive reliance on tools without testing in the real world.
- Not engaging business teams, which results in a lack of alignment of priorities.
- Poor access control testing, particularly in the case of third parties.
By preventing these pitfalls, businesses can have a realistic and scalable cybersecurity plan that is focused on actual risks.
As organizations strengthen their data risk management strategies, staying updated with evolving threats and best practices is essential. For a deeper understanding, explore the latest USCSI® insight on “Data Security: Protecting Digital Information in the Modern Era.”
The Way Forward
A data risk assessment is not just a task but a continuous ability. Organizations should move from reactive security to proactive but intelligence-based approaches, with risk decisions made in line with business impact.
Meanwhile, it is necessary to develop effective cybersecurity skills and become a certified expert with the right cybersecurity certification. Programs like the United States Cybersecurity Institute (USCSI®) and its Certified Senior Cybersecurity Specialist (CSCS™) certification help professionals develop practical expertise in data security and enterprise risk management.
Finally, data risk management is concerned with the possibility of using data in a fast-changing digital environment securely and with confidence.