Top 10 IT Security Frameworks and Standards to Watch in 2026
If you work in the field of cybersecurity, you’re already aware that the threats around you don’t take a break. All it takes is one forgotten patch, one weak password, or even just one successful social engineering attack to turn your whole day upside down.
This is why you simply can’t afford to live on guesswork — what you need is structure, clarity, and solid security frameworks with demonstrated durability around your systems.
In this blog, you will learn the top 10 IT security frameworks that every cybersecurity professional, IT staff member (or chief security officer or infosec manager) needs to know. Let’s get started.
What is IT Security Framework?
Think of a cybersecurity framework as a safety playbook for your digital world. It explains to you the smartest moves to protect your systems before attackers even set foot on the field.
When organizations were asked to respond to this question according to the Global Cybersecurity Outlook 2025 of the World Economic Forum:
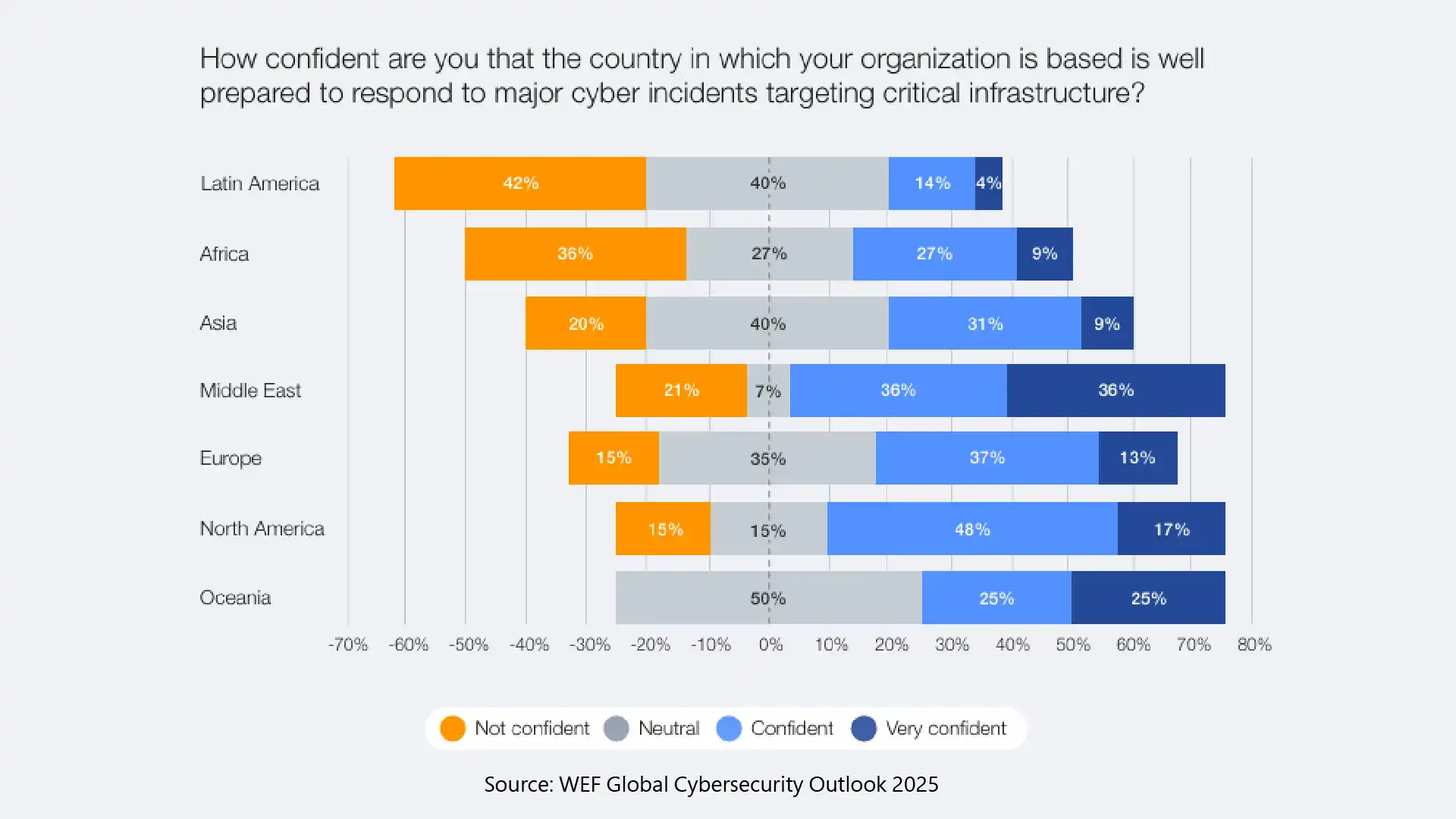
This data shows that organizations in countries from Asia to Europe are still in urgent need of the right information security framework to safeguard them.
Benefits of IT Security Frameworks in 2026
As per Accenture’s recent State of Cybersecurity Resilience 2025 Report, around 92% of organizations struggle with essential resilience-building efforts, such as pressure-testing defenses, understanding emerging threats, and establishing rapid response mechanisms.
For the above purposes, organizations are adopting IT security standards that provide:
- Clear Structure: It provides your team with a clear, systematic approach to managing information security threats.
- Better Defense: It closes an attack surface that attackers frequently target, particularly during social engineering and system compromise.
- Regulatory Confidence: It ensures your compliance and enables you to demonstrate your security posture to auditors and customers.
- Faster Recovery: It directs your response when something breaks so that your downtime is minimal and your reputation remains untarnished.
Top 10 IT Security Frameworks You Shouldn’t Miss
Here are the 10 top infosec frameworks that are powering the modern information security system:
-
NIST Cybersecurity Framework: Your Core Security Playbook
If you’re constructing a security foundation, this will be your jumping-off point. The NIST CSF distills your job into five easy-to-understand actions: Identify, Protect, Detect, Respond, and Recover. This provides you with a straightforward map for how cybersecurity tools, policies, and operations can be arranged.
So, whether you’re an IT security consultant in a small business or a responsible chief information security officer, NIST is flexible without being overly prescriptive. It enables you to focus on the risks that matter while reducing waste and making better-informed security decisions.
-
ISO 27001: The Global Gold Standard in Information Security
If your organization serves overseas customers, the ISO 27001 security framework is a must. It enables you to develop an entire information security management system that is audited and certifiable.
With this security framework, you’ll focus on:
- Risk assessment
- Security controls
- Incident response planning
- Continuous monitoring
ISO 27001 builds trust with partners and customers, and it is one of the most well-respected Infosec frameworks for any organization.
-
CIS Controls: Practical, Fast, and Perfect for IT Teams
CIS Controls provide you with 18 prioritized and effective actions that you can concentrate on to secure your environment, without the need for theory or confusion. When they want quick, trackable boosts, IT teams apply them.
Key controls include:
- Asset inventory
- Vulnerability management
- Email and browser protection
- Access control
CIS is a great option for blocking everyday threats, such as phishing and malware-ridden websites, as you work up to more advanced security templates.
-
SOC 2: Essential for SaaS and Cloud-First Companies
If your business holds or processes customer data in the cloud, SOC 2 is not optional. It is centered on five trust principles: security, availability, processing integrity, confidentiality, and privacy.
If we talk about compliance, even when you’re thinking about audits from the early stages of your business, a security framework like SOC 2 is a long-term play. Achieving the SOC 2 framework demonstrates your commitment to protecting highly sensitive data and positions your organization as a trusted partner in the market.
-
PCI DSS: Mandatory for Any Business Handling Payment Data
If you are ever working with credit or debit card information, PCI DSS is a mandatory framework for businesses that handle payment or transaction data. Its controllers minimize the risk of attack in the payment environments.
It will help in securing cardholder data, restricting who can access systems, keeping firewalls updated, and logging activity. PCI DSS is strict because it helps organizations stay a step ahead of the cybersecurity attackers.
-
HIPAA Security Rule: Protecting Healthcare Data
If you work in hospitals, clinics, insurance, or digital health, HIPAA is your dominion. It shapes the way you secure electronic health records against unauthorized access.
You’ll concentrate on administrative, physical, and technical safeguards that will be in place to maintain the trust of your patients.
Healthcare continues to be among the most targeted industries by ransomware, and HIPAA’s fines have never been more important.
-
COBIT: Where Security Meets Business Strategy
COBIT is there to aid you with linking Information security with your organisation’s business aims. NIST and CIS are focused more on technical controls, whereas COBIT provides direction in governance and decision-making.
It’s great when you are working with leadership or reporting to the board. It demonstrates the economic value IT security frameworks provide to revenue, trust, and sustainable growth.
-
MITRE ATT&CK: The Ultimate Threat Behavior Map
MITRE ATT&CK lets you see how the attackers work, step-by-step, from when they get into your system to what damage they try to do.
Who uses MITRE ATT&CK?
- Build sharper, threat-focused detection rules
- Boost observation of all endpoints and networks
- Conduct more precise and proactive threat-hunting exercises
MITRE enables you to view attacks the way adversaries stage them, in order to detect faster and respond with precision.
-
Zero Trust Architecture: Never Trust, Always Verify
Zero Trust is not a single framework — it’s a mentality around security. It treats every outside- or inside-network access request as if it is potentially malicious.
Zero Trust needs strong authentication, continuous monitoring, and micro-segmentation. As security AI matures, the ability for Zero Trust to integrate with automation solutions that analyse user behaviour in real time.
-
CMMC: Required for U.S. Defense Contractors
If your business does work for the U.S. Department of Defense, you don’t have a choice when it comes to the Cybersecurity Maturity Model Certification (CMMC); you have and will have to comply with this new set of information security standards. CMMC assesses your readiness to safeguard Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) at various levels of maturity.
The framework is designed to ascertain whether your processes, controls, and everyday practices actually protect sensitive defence data. It’s designed to help you:
- Prevent leaks of mission-critical information
- Demonstrate that you can meet stringent federal security standards
- Create cyber resilience that lasts, rather than just passing a compliance checkpoint
Put simply, CMMC makes sure you’re trustworthy enough to join the national defense supply chain.
The Bottom Line
When you master these IT security frameworks, you're not just relying on the more reliable IT security standards but also helping your organization stay ahead of cyber attackers.
If you want to lead in the field of cybersecurity or aim to become a chief security officer, the right cybersecurity leadership certification, such as the Certified Senior Cybersecurity Specialist (CSCS™) of USCSI®, can help you learn about this certification and train you to lead with confidence and competence.
Choose one framework aligned with your business environment and start implementing it today. Strong security always begins with one informed, strategic move ahead.